Ekubo Protocol Exploit: WBTC Hack and Token Approval Risk
Table of Contents
Table of Contents
Share

Ekubo Protocol lost 17 WBTC in a May 2026 ACT exploit. Audit your DeFi router contract for token approval access control gaps before the next attack hits.
Frequently Asked Questions
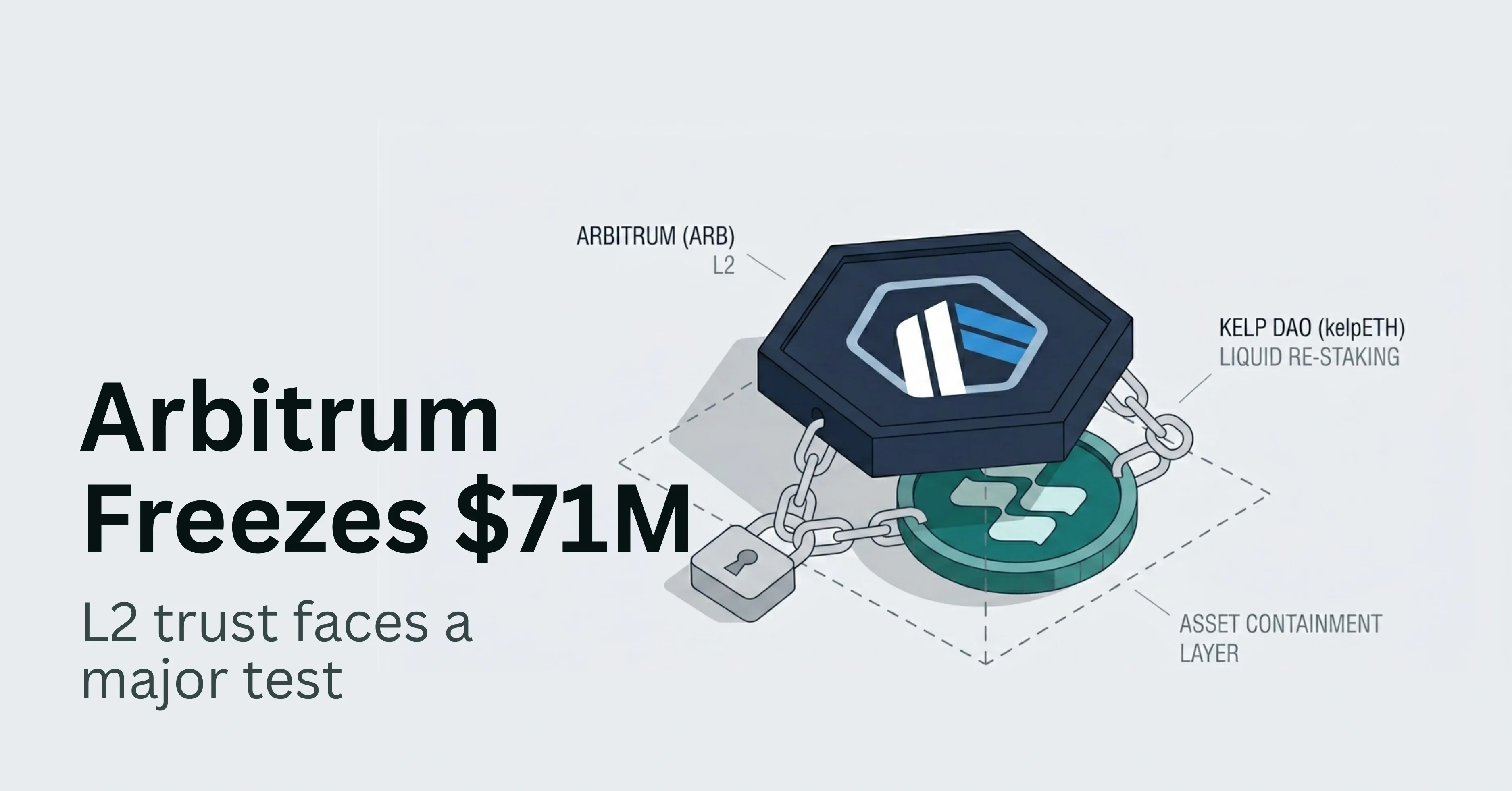
- The Ekubo Protocol exploit occurred because EVM swap router contracts (Ethereum V2: 0x8ccb1ffd5c2aa6bd926473425dea4c8c15de60fd, Ethereum V3: 0x4f168f17923435c999f5c8565acab52c2218edf2, Arbitrum V3: 0xc93c4ad185ca48d66fefe80f906a67ef859fc47d) did not verify whether the caller of payCallback was the authorized lock initiator. This allowed an attacker to enter the Core lock flow, withdraw WBTC via the withdraw function, then repay the debt by calling payCallback which in turn called transferFrom against a victim address that had previously granted an ERC-20 approval to the router. The attacker drained approximately 17 WBTC across multiple transactions before the team issued a revocation advisory.
- The Approved Controllable TransferFrom (ACT) vulnerability class exploits contracts that call transferFrom(victim, destination, amount) without confirming that the current transaction was initiated by the victim. Any user who has granted an ERC-20 allowance to the vulnerable contract becomes a potential victim. An attacker calls an external entry point such as payCallback, which internally calls transferFrom using the victim address as the source. The contract never checks whether the victim consented to this specific transfer. The fix requires adding a lock-initiator whitelist check before any transferFrom execution path in the contract.
- CTOs should immediately audit every function in the router that calls transferFrom and verify that each such call is gated by an explicit check confirming the msg.sender is the authorized session initiator or an allowlisted payer. Any function reachable externally that invokes transferFrom with a non-msg.sender source address is a critical vulnerability. After fixing the access control, replace unlimited ERC-20 approvals with per-transaction EIP-2612 permit-based signatures to eliminate residual approval exposure. Finally, deploy a real-time monitor on the payCallback or equivalent function to detect and block anomalous drain patterns before they reach material loss.
Don't Miss What's Next
Subscribe to newsletter
DeFi Security
Smart Contract Audit
Token Approvals
Ekubo Protocol
EVM Exploit
Get in Touch
Our team will get back to you within 24 hours.